Update
On August 1, 2016, Blue Coat, Inc. (K9’s parent company) was acquired by Symantec™. As can be imagined Blue Coat and Symantec had a handful of similar products and unfortunately, it didn’t make sense to maintain two competing products. it was decided to “end-of-life” K9 Web Protection.
Effective immediately, K9 Web Protection is no longer available for purchase or download. Technical Support for K9 will end on June 30, 2019.
It is unfortunate to see K9 Web Protection go. I am not aware of an alternative free software that provides the same level of protection at a premium quality. However, for those interested in alternatives to K9 Web Protection, I would recommend you can start with Quad9 and OpenDNS Home. While neither of them provides everything that K9 did, but they still protect your system against most common online threats.
“We may think one layer of security will protect us – for example, antivirus. Unfortunately for that approach, history has proven that, although single-focus solutions are useful in stopping specific attacks, the capabilities of advanced malware are so broad that such protections inevitably fail.” – Jerry Shenk, Layered Security: Why It Works.
Making use of layered security for personal use is of the utmost importance as I have covered a couple of times in the past: here, here, and here. Just as I have done in the past, I will use this post to share another tool that you can explore to support your personal layered security strategy.
My never-ending curiosity to explore and test new technologies can sometimes lead me to stumble upon genuinely impressive solutions. Fortunately for you, I believe this tool falls into that category.
K9 Web Protection is the software that I have been testing for some months now, and I must say, I’ve been truly pleased with its results. The software falls under the Web Filter category, which places a restriction on websites that you can visit. Web Filtering is used in two major cases. The first is to permit parents to control the sort of content accessible to their children, offering their kids a safe environment to learn and explore online. The second is for businesses who wish to prevent their employees from accessing websites that do not pertain to their jobs.
However, in addition to the above-mentioned, from my experience using this software on a daily basis, I have come across other benefits:
- Real-time malware protection“helps identify and block illegal or undesirable content in real time, including malware-infected sites. You also benefit from the WebPulse cloud service, a growing community of more than 62 million users who provide more than six billion real-time Web content ratings per day.”
- You can learn more about web filtering and intelligence here.
- Automatic content ratings“New websites and web pages are created every minute, and no one person can possibly rate or categorize all of them. To ensure protection against new or previously unrated websites, Blue Coat’s patent-pending Dynamic Real-Time Rating™ (DRTR) technology automatically determines the category of an unrated web page, and allows or blocks it according to your specifications.”
Another advantage of the K9 Web Protection is that it is backed by Blue Coat (acquired by Symantec in 2016), the leader in Web Security “with an impressive portfolio of integrated technologies serving as a trusted platform to deliver Cloud Generation Security to more than 15,000 customers worldwide.”
This solution is truly an “enterprise-class security software designed for home computers.” Also, did I mention that it’s free! “As part of the Blue Coat Community Outreach Program, K9 Web Protection is free for home use. You can also purchase a license to use K9 Web Protection for business, government, non-profit, or other use.”
I will do a quick overview of the installation and usage of the software, but you can find a well-documented quick start guide and user manual here:
Installation and Usage Overview:

- The installation process should take a couple of minutes to complete as it is self-explanatory.
- Upon completion, the application’s interface will open in your browser:

- To view or modify any of the configurations, you will be prompted to enter the password you created during installation.
- Here are some of the options and details you can access from the Setup page:

- Web Categories to Block: choosing one of the available levels allows you to block selected categories of websites.
- Time Restrictions: 3 options are available to block web access depending on the time of day. Unrestricted places no restrictions on web access. NightGuard blocks all web access during contiguous blocks of time every day. Custom enables you to choose days of the week and time periods to block all web access.
- Web Site Exceptions: Allows you to create lists of websites to “always block” or “always allow.” Blocking Effects: “Bark When Blocked” plays a barking sound when a web page is blocked. Make sure the sound is enabled and not muted. Show Admin Options displays options on blocked web pages which enable administrators to view the blocked web page. Enable Time Out allows you to block all web access if too many web pages are blocked in a given period of time
- URL Keywords: Allows you to enter keywords which, if found in a URL, cause a “block page” to display. Safe Search: “Redirect to K9 Safe Search” will redirect searches to various search engines through K9’s Safe Search. This provides a safer search experience than other search engines provide. Force Safe Search will prevent users from disabling Safe Search functionality provided by various websites.
- Other Settings: “Update to Beta” enables you to get advance copies of new K9 Web Protection software undergoing development. Blue Coat distributes Beta versions so that K9 gets used in “real world” environments before being released as a final version. Please note that Beta versions might be incomplete and less stable than final versions. “Filter Secure Traffic” enables K9 to block secure websites (i.e. sites that use the HTTPS protocol).
- Password/Email: Allows you to change your K9 administrator password or e-mail address.
- K9 Update: Installs software updates if available.
- View Activity Summary: This tab shows a summary of all “Web Activity” on your computer: To view more details, click the “Category” or “Requests” links. On these pages, you have the option of grouping the data by month or by day. To view Administrative Events details, click the “View All” link. (Some of these activities are as a result of automatic browser and toolbar updates, for example, and might display URL formats with which you are not familiar.) By selecting “Clear Logs”, all your activity data will be cleared; however, three days’ worth of administrative events will be retained.

As you can see from the above, the information provided here is extremely granular and it allows you to not only get an easy view of your browsing behavior but also the behaviors of the various system and application components. I have been using this solution in conjunction with other traditional protective mechanisms, such as anti-virus, and the benefits have been massive.
For instance, sometimes, while surfing the internet, I would see a certain URL get blocked or a visit history to a certain category in a website without a recollection of visiting that website. However, after investigations, I found that some components of a software installed on my computer or an extension in my browser is the reason behind that activity.
“The malware ecosystem has changed drastically in the past 10 years, to the point that the old precautions are just no longer enough” – Malwarebytes LABS. I have been using K9 Web Protection on many of my personal computers because I have been impressed with it, so I thought to share it here. I believe it provides that extra layer of protection that we can all appreciate in a world where cyber threats are on the rise. In addition, I believe this solution is a wonderful option for those that are less familiar with common cyber threat vectors (i.e. parents) and can easily fall for phishing emails or click on an adware as they browse the internet.
As we have known for some time, “there is no single solution for the information security problems we face today. A combination of many different kinds of security tools is required to protect you from modern threats…” and I believe K9 Web Protection is among the best tools we have today, so you should definitely equip yourself with it if you are going to create a safe web environment for yourself, your kids, your employees, and everyone around you!
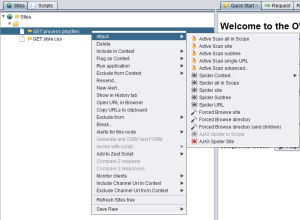
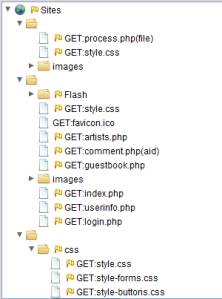 After you have the site structure similar to the above, you can take your test in several different directions — most of which can be viewed by simply right-clicking on any of the site’s pages:
After you have the site structure similar to the above, you can take your test in several different directions — most of which can be viewed by simply right-clicking on any of the site’s pages: