
I want to write a follow-up on my last post about chain-of-commands not properly being captured by many defensive tools. During further research and testing, I observed that built-in Windows Command line actions are also not captured.
For instance, a simple act of deleting a file from the CMD Command-line is neither captured in SYSMON or in Windows Event logs:
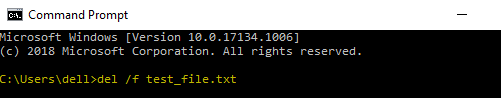
CMD.EXE > del /f test_file.txt
The only event observed in SYSMON for the above action was the following:
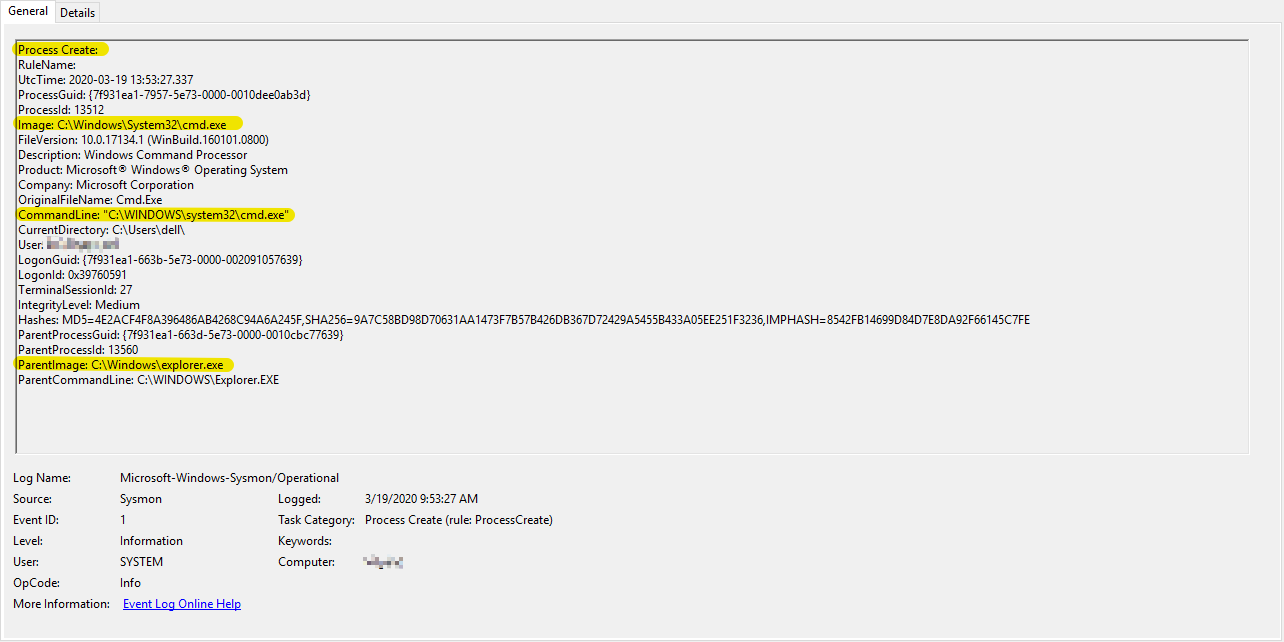
Additionally, nothing notable was observed in Windows Event logs.
This simple act of deleting a file is a common technique used by the adversaries. This action could be done both manually or through malware. One example where this technique is used is in the case of the Robbinhood Ransomware. In this sandbox report, you can see various quite-delete operations that Robbinhood malware executes.
I understand that there are other means of extracting CMD Command-line execution content. However, many of those require digital forensics analysis.
For instance, you can review Command-line history by analyzing the memory capture using a tool such as Volatility with plugins: cmdscan, consoles or just running strings against the memory image. However, this type of analysis requires either a memory image capture or a specialized commercial solution that can scan live memory content (example). Unfortunately, most organizations do not have access to these enterprise-solutions thus their ability to hunt for such Command-line techniques becomes limited.
MITRE ATT&CK Evaluations also has an entry for this technique 9.C.4 File Deletion where you can select various technologies from the drop-down list and see how they detect this technique.
If you are collecting and hunting full CMD Commandline, I would love to hear about your feedback; especially, if the technology/method that you are using is not one of the ones tested in ATT&CK Evaluations above.
https://attackevals.mitre.org/technique_comparison.html?round=APT29&step_tid=9.C.4_T1107&vendors=
